Книга: Fedora™ Unleashed, 2008 edition
The FTP User
Разделы на этой странице:
The FTP User
After Fedora is installed, an FTP user is created. This user is not a normal user per se, but a name for anonymous FTP users. The FTP user entry in /etc/passwd looks like this:
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
NOTE
The FTP user, as discussed here, applies to anonymous FTP configurations and server setup.
Also, note that other Linux distributions might use a different default directory, such as /usr/local/ftp, for FTP files and anonymous users.
This entry follows the standard /etc/passwd entry: username, password, user ID, group ID, comment field, home directory, and shell. To learn more about /etc/password, see the section "The Password File" in Chapter 10, "Managing Users."
Items in this entry are separated by colons. In the preceding example, you can see that the Fedora system hosting the server uses shadowed password because an x is present in the traditional password field. The shadow password system is important because it provides Fedora an additional level of security; the shadow password system is normally installed during the Fedora installation.
The FTP server software uses this user account to assign permissions to users connecting to the server. By using a default shell of /sbin/nologin (as opposed to /bin/bash or some other standard interactive shell) for anonymous FTP users, the software renders those users unable to log in as regular users. /sbin/nologin is not a shell, but a program usually assigned to an account that has been locked. As root inspection of the /etc/shadow file shows (see Listing 20.1), it is not possible to log in to this account, denoted by the use of * as the password.
LISTING 20.1 Shadow Password File ftp User Entry
# cat /etc/shadow
bin:*:11899:0:99999:7:::
daemon:*:11899:0:99999:7:::
adm:*:11899:0:99999:7:::
lp:*:11899:0:99999:7:::
...
ftp:*:12276:0:99999:7:::
...
The shadow file (only a portion of which is shown in Listing 20.1) contains additional information not found in the standard /etc/passwd file, such as account expiration, pass word expiration, whether the account is locked, and the encrypted password. The * in the password field indicates that the account is not a standard login account; thus, it does not have a password.
Although shadow passwords are in use on the system, passwords are not transmitted in a secure manner when using FTP. Because FTP was written before the necessity of encryption and security, it does not provide the mechanics necessary to send encrypted pass words. Account information is sent in plain text on FTP servers; anyone with enough technical knowledge and a network sniffer can find the password for the account to which you connect on the server. Many sites use an anonymous-only FTP server specifically to prevent normal account passwords from being transmitted over the Internet.
Figure 20.1 shows a portion of an ethereal capture of an FTP session where you can see it has caught a user's password being sent in clear text. The ethereal client is a graphical browser used to display network traffic in real time, and it can be used to watch packet data, such as an FTP login on a LAN.
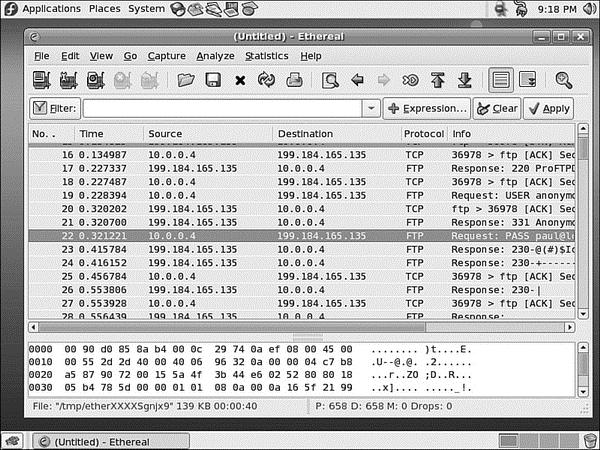
FIGURE 20.1 The ethereal client can filter and sniff FTP sessions to capture usernames and passwords.
Quick and Dirty FTP Service
Conscientious Linux administrators take the time to carefully install, set up, and configure a production FTP server before offering public service or opening up for business on the Internet. However, you can set up a server very quickly on a secure LAN by following a few simple steps:
1. Ensure that the FTP server RPM package is installed, networking is enabled, and firewall rules on the server allow FTP access. See Chapter 14, "Networking," to see how to use Red Hat's system-config-securitylevel client for firewalling.
2. If anonymous access to server files is desired, populate the /var/ftp/pub directory. Do this by mounting or copying your content, such as directories and files, under this directory.
3. Edit and then save the appropriate configuration file (such as vsftpd.conf for vsftpd) to enable access.
4. If you are using wu-ftpd, you must start or restart xinetd like so: /etc/rc.d/init.d/xinetd restart. If you are using vsftpd, you must start or restart the server like so: service vsftpd start.
- Choosing an FTP Server
- Installing FTP Software
- The FTP User
- xinetd Configuration for wu-ftpd
- Configuring the Very Secure FTP Server
- Configuring the wu-ftpd Server
- Using Commands in the ftpaccess File to Configure wu-ftpd
- Configuring FTP Server File-Conversion Actions
- Using ftphosts to Allow or Deny FTP Server Connection
- Using Commands for Server Administration
- Reference
- The SSH Tools
- Using sftp to Copy Many Files Between Machines
- Other FTP Servers
- Starting the Very Secure FTP Server (vsftpd) Package
- Configuring the Very Secure FTP Server
- Other vsftpd Server Configuration Files
- Configuring the wu-ftpd Server
- Using Commands in the ftpaccess File to Configure wu-ftpd
- Configure Commands Directed Toward the cdpath
- Count the Number of Connections
- Documentation Available via FTP
- 4.4.4 The Dispatcher